Researchers in Morocco analyzed cybersecurity challenges in smart grids, highlighting AI-driven detection and defense strategies against threats such as distributed denial-of-service, replay false data injection, and IoT-based attacks. They recommend multi-layered protection, real-time anomaly detection, secure IoT devices, and personnel training to increase resilience and protect power system operations.
Researchers from the Higher Technical School of Morocco, Moulay Ismail Universityhave conducted a comprehensive analysis of emerging cybersecurity challenges in energy systems and detailed recent developments in detection and defense strategies.
Their work highlights the growing role of AI in improving control, protection and resilience in modern smart grids. It also classifies cyber threats based on origin, impact and affected system layers to provide a structured insight and assesses machine learning and optimization-based intrusion detection systems (IDSs) for power systems.
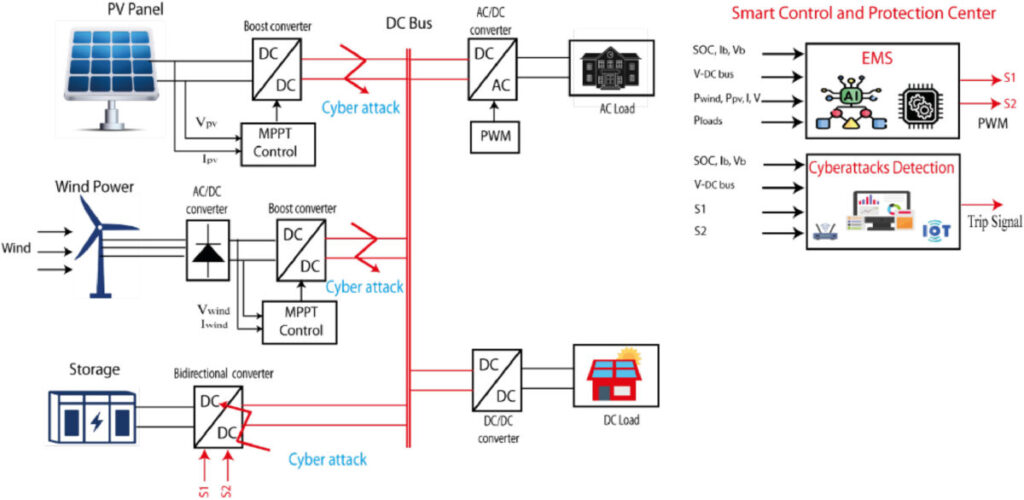
The researchers highlighted that renewable smart grids face several cyber threats that can disrupt operations and compromise data. For example, distributed denial-of-service (DDoS) attacks flood networks with traffic, blocking legitimate access and slowing control actions, while data integrity attacks manipulate sensor or control data and cause incorrect decisions or blackouts.
Additionally, replay attacks retransmit intercepted data to confuse the system, and spoof data injection attacks subtly alter real-time data to mimic normal activities while disrupting the power grid. Stealthy attacks inject hidden signals that manipulate system behavior without detection, while attacks on IoT devices exploit vulnerabilities in meters or sensors to spread malware, steal data or conduct DoS attacks.
Finally, zero dynamics attacks use system models to generate hidden signals that leave output measurements unchanged but impact operations, creating advanced stealth threats to smart grid security.
Do you want to strengthen and improve the cybersecurity of your solar assets to protect them from emerging threats?
Visit us on April 29 for pv magazine Webinar+ | Deciphering the first large-scale cyber attack on Europe’s solar energy infrastructure – The Case of Poland and Lessons Learned
The researchers warned that while smart grids have improved energy efficiency and flexibility through advanced communications and distributed energy resources, they have also introduced new cyber vulnerabilities. Threats such as phishing, malware, denial-of-service (DoS) attacks and false data injection (FDI) can disrupt business operations, compromise data and damage infrastructure.
They recommend implementing defense strategies that maintain confidentiality, integrity, and availability, while also integrating authentication, authorization, privacy, and reliability. Machine learning and data-driven intrusion detection systems can help identify anomalies and detect FDI attacks in real time, especially in smart grids and industrial control systems such as SCADA, which rely on accurate sensor measurements for condition estimation.
The research team also encouraged energy asset owners and network operators to implement substation security measures and protocol vulnerability assessments to detect risks at the hardware and network levels. Blockchain, distributed ledgers, and Hilbert-Huang transformation methods are highlighted as tools to further strengthen cybersecurity.
IoT devices, including sensors and smart meters, must be secured with strong authentication, secure boot procedures, frequent firmware updates, and standardized security across manufacturers. Sensitive network data must be protected using techniques such as homomorphic encryption to maintain confidentiality during storage and transmission.
“A multi-layered security approach that includes firewalls, intrusion detection systems and network segmentation can increase network resilience. Extracting critical elements from vulnerable IoT devices and leveraging redundant control channels ensures operational continuity during attacks,” the researchers said.
Machine learning and anomaly detection systems should be deployed to enable real-time identification of irregular activities, including foreign direct investment and the spread of malware. Standardized protocols and rapid incident response measures should also support collaboration between network operators, IoT manufacturers and regulators, facilitated by information sharing platforms.
The researchers emphasize that human-targeted attacks, including phishing and social engineering, remain significant threats but can be mitigated with regular staffing and user training.
The review was presented in “Cybersecurity challenges and defense strategies for next-generation energy systems”, published in Cyber-physical energy systems.
This content is copyrighted and may not be reused. If you would like to collaborate with us and reuse some of our content, please contact: editors@pv-magazine.com.