In an interview with pv magazineCybersecurity expert Mohammad Al Faruque explains how seemingly simple sensors in PV systems and other energy systems are surprisingly vulnerable to magnetic, electrical and acoustic disturbances, which can affect remote control systems without physical access. Protecting these sensors requires both strict physical security and the development of hardened, interference-resistant technology to protect critical infrastructure.
In recent years, researchers have increasingly focused on cyber-physical systems, where hardware and software interact in complex ways, and the vulnerabilities that can flow through multiple layers of these systems. A recent area of interest is sensors, the ubiquitous devices embedded in everything from industrial control systems to inverters used in PV systems, whose safety has long been overlooked.
With the explosion of Internet-of-Things (IoT) devices and connected infrastructure, sensors have become critical but surprisingly vulnerable components. Many of the sensors used in power systems are based on old technology, but safety concerns have historically been minimal. Recently, however, researchers have begun examining these sensors for potential weaknesses, revealing surprising vulnerabilities.
“Sensors can be easily disrupted by creating electric, magnetic and acoustic fields,” said Mohammad Al Faruque, director of the Center for Resilient Autonomous Systems at the University of California and Conexant-Broadcom Endowed Chair in the Department of Electrical Engineering and Computer Science. pv magazine. “You don’t actually have to go into the system because you can create a magnetic field around the system that can lead very gently to the control layer. Inverters in PV systems have current and voltage sensors that are connected directly to the controller that controls the system. It’s so easy to create a magnetic field and disrupt these sensors.”
According to Al Faruque, potential attackers could generate a controlled magnetic field that directly affects the inverter’s sensors. The resulting disruption can affect the control system, all without touching the inverter itself. “By manipulating the surrounding environment, attackers can subtly alter sensor measurements, which in turn can reach the control layer of the system,” he explains. “We tested this with a simple setup: a magnet combined with inexpensive electronics worth about $45. This included an Arduino Uno, a few MOSFETs, a Zigbee RF module, an ultrasonic sensor, and batteries. In short, it was a simple combination of signal processing and electronic control.”
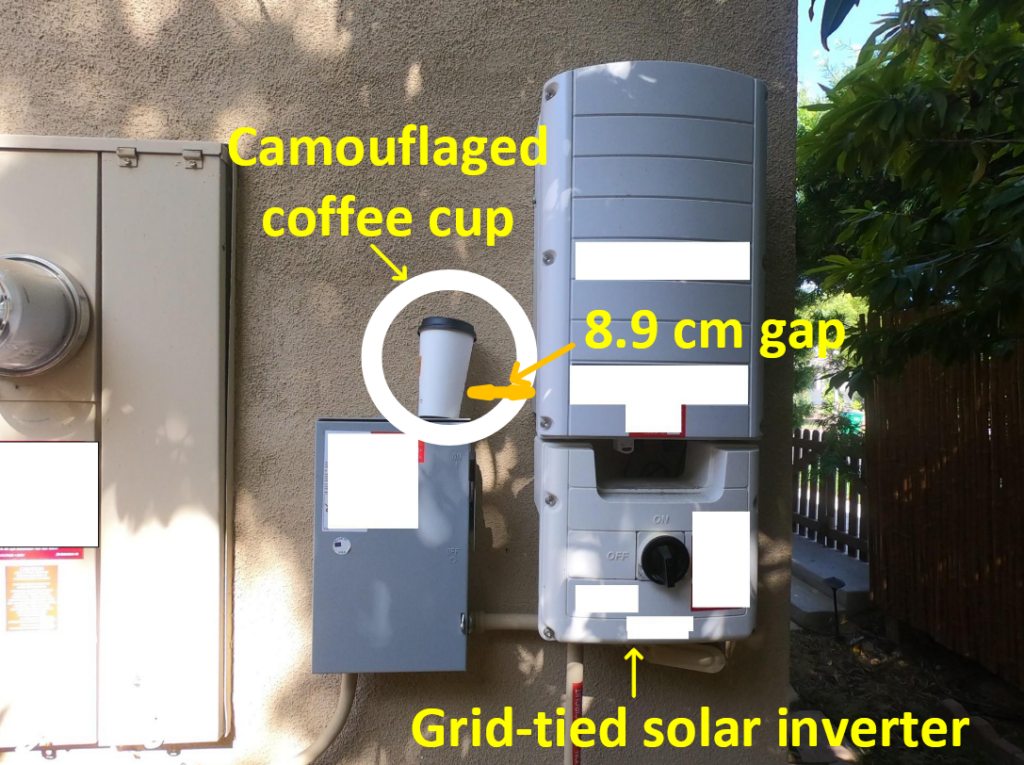
Al Faruque and his team built a compact controller and integrated it into a coffee mug, making it easy to place in everyday objects or even environmental waste for testing. The circuit had a radio module so it could be connected to a computer. This allowed the researchers to turn it on remotely and control the magnetic field it generated. “By carefully adjusting the controller, we were even able to regulate the strength of this magnetic field,” says the cybersecurity expert. “These controlled magnetic field changes in turn affected nearby current and voltage sensors. Essentially, this setup shows us how electromagnetic disturbances interact with electronic systems in a measurable way.”
Image: University of California
“This is easier than most people imagine,” he continued. “You don’t need to physically open the Remote Terminal Unit (RTU) or other controllers. If you just have a device nearby, which is properly designed, you can manipulate the sensor readings remotely via wireless communication. Any energy infrastructure must be physically protected. We cannot be naive enough to assume that anything left behind is harmless; it could very well be malicious.”
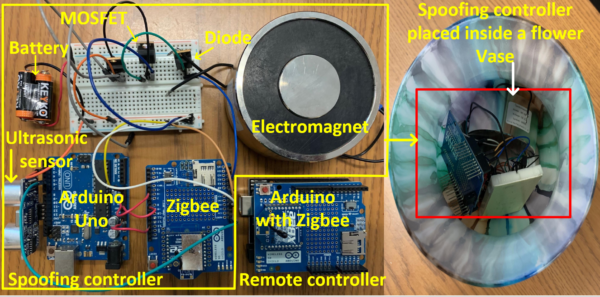
Image: University of California
“Someone could deliberately leave a coffee mug near an inverter as a form of camouflage,” Al Faruque said. “At first glance it seems harmless, but the device inside the mug may contain a radio or communications module, allowing remote access from anywhere in the world. That is why physical protection of PV installations is so important. An attacker can plant seemingly innocuous objects, such as environmental waste, that are actually embedded with technology that can generate magnetic fields or other disruptions. In the future, such attacks could even be carried out remotely using drones, without anyone having to be physically present.”
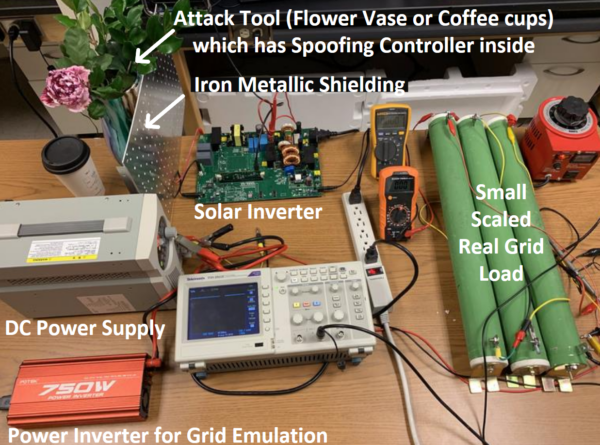
Image: University of California
Securing inverter sensors requires both physical security, such as access controls and environmental monitoring, as well as technological innovation. Solutions include the development of secure sensors that can detect or resist external interference, although these come at a higher cost.
The research team began developing secure sensors, including specialized Hall sensors, that can withstand magnetic or environmental interference. However, these solutions are more expensive and the question is whether the industry is prepared to invest preventively in security. Many organizations are reluctant to spend money unless there is a clear vulnerability or incident. Furthermore, most incidents of these types of attacks are likely to go unreported unless they become a national-level problem.
“I am not aware of any reported cases so far,” the scientist said. “These vulnerabilities are mainly potential risks for the time being, and that is why I emphasize that sensors in PV installations are a critical vulnerability. Every PV installation must be considered part of critical infrastructure and their environment must be protected accordingly. Of course, implementing this level of protection is not easy or cheap. But given the geopolitical tensions and the growing need for security, I believe it will become increasingly necessary.”
In the short term, raising awareness among plant operators, implementing physical security measures and conducting regular inspections are essential. In the long term, the industry must push for technological improvements in sensors, controllers and safe design practices to protect critical infrastructure.
“As our energy systems become increasingly complex and interconnected, the humble sensor, once taken for granted, is emerging as a critical point of vulnerability. Addressing these risks is not just about preventing theft or downtime; it is about protecting the integrity of the energy network itself,” concludes Al Faruque.
This content is copyrighted and may not be reused. If you would like to collaborate with us and reuse some of our content, please contact: editors@pv-magazine.com.
Popular content